Mac OS X version 10.0 shipped on March 24, 2001, and in over a dozen years, the platform has proven particularly resilient to malware. Not that malware for the Mac doesn’t exist, just that it never seems to get any traction.
The latest one has been getting some press this week, as is always the case when someone finds a way to hack the Mac. According to sources, this one exploits a 5-month-old security flaw tied to the Unix sudo command. According to most reports, it only impacts those using OS X 10.7 Lion through 10.8.4 Mountain Lion (TenFourFox Development Blog says it could potentially apply all the way back to OS X 10.4 Tiger, and it also provides a way to protect your Mac), and then only users with admin status.
On top of all that, the OS X 10.7-10.8.4 user with admin status must have already run sudo in the current session, although it could also be run by applications or remotely.
We have no information regarding the vulnerability of OS X 10.9 Mavericks, which is nearing commercial release.
MacNN states:
“The possibility of an attacker successfully exploiting the vulnerability is pretty remote under most circumstances, but there are situations where the various requirements could be met, and the attack successful.”
Wow, that’s a lot of hoops to jump through just to be vulnerable to the attack. Seriously, when is the last time you used sudo on your Lion or Mountain Lion Mac?
You’re probably safe from this exploit, but there are steps you can take to make sure your Mac is safe from it.
How It Works
This exploit takes advantage of an authentication bypass vulnerability that was reported in March. Sudo is designed to require a user password, and if you’ve already run sudo in the Terminal, you could be at risk, because Terminal remembers your password and does not log you out.
By accessing sudo after it’s been accessed by someone with an admin account, this bit of code resets the computer’s clock to 1970.01.01, the beginning of the Unix epoch. And once that’s been done, it can achieve super user status, giving it access to all user accounts on your Mac’s hard drive. This is a Mac-specific problem, because while most Unix and Linux distributions require a password to change the system clock, OS X does not.
Finally, the attacker has to have physical access to your Mac or remote access to it.
Who Is Safe?
You’re pretty safe to begin with.
If you’re not running with admin privileges, you have nothing to worry about.
If a potential attacker does not have physical access to your Mac and you have remote access disabled, you have nothing to worry about.
If you’re still running OS X 10.6.8 Snow Leopard or earlier, you may be safe, as this exploit is only reported to work with 10.7 Lion and 10.8 Mountain Lion. Then again, OS X 10.4 and later all use versions of sudo that can be exploited. See directions below for securing any version of OS X against this exploit.
Even if you haven’t used sudo in the Terminal, you could still be in danger.
How to Make Your Mac Safe
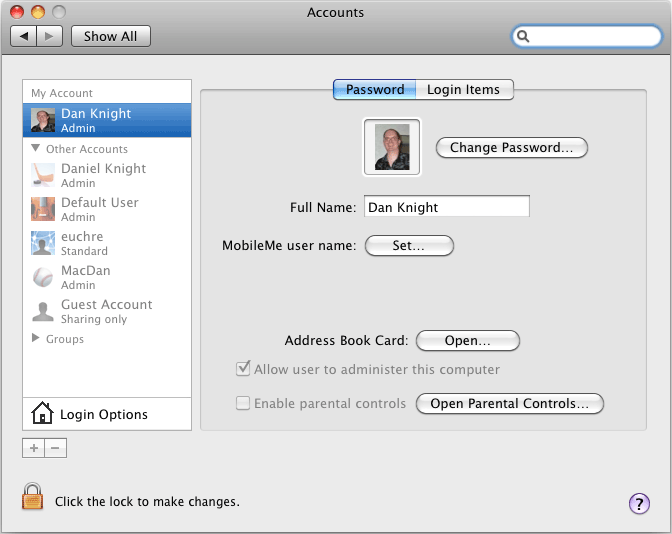
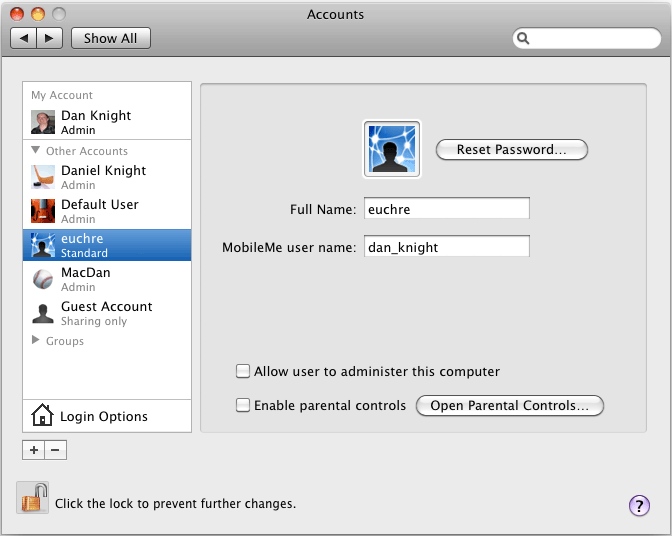
The easiest way to be secure is to work from a standard user account, not an admin account. To change a user account from admin to standard:
- Log in from another admin account. Your Mac needs to have a least one, but you really don’t need to be using it for your day-to-day work.
- Open System Preferences.
- Open Accounts.
- Click on the lock icon and enter the admin password.
- Select the admin user account you want to change and deselect “Allow user to administer this computer”.
- Repeat for any other user accounts you want to downgrade from admin.
To secure your admin accounts, follow these instructions from our friends on the TenFourFox team:
- Run Terminal.
- Type sudo visudo and enter your root password.
- Add this line to the configuration file: Defaults timestamp_timeout=0 [that’s a zero]
- Save the file and exit terminal.
With this modification, your Mac will not change system time without asking for your root password. This has been tested on both OS X 10.4 and 10.6, and it should work with any version since 10.4.
Further Reading
- CVE-2013-1775, Mitre.org, 2013.02.19
- Unpatched Mac Bug Gives Attackers “Super User” Status by Going Back in Time, Dan Goodin, Ars Technica, 2013.08.28
- Flaw in Unix sudo Command Threatens OS X, Linux, MacNN, 2013.08.28
- Security Notes: Sudo and OS X, More Reasons You Should Not Use Java, TenFourFox Development Blog, 2013.08.29
Keywords: #sudypasswordbypass #macvulnerability
Short link: http://goo.gl/LSXDv9