One of
the most interesting perks of using Mac OS X is benefiting from a
strong amount of security that Windows users don't enjoy - and
without sacrificing the "mainstream" aspect of the Mac.
On the other hand, a bit of paranoia is healthy as far as
security is concerned. There are ways to satisfy your need for
secure computing, and most of them are little things that can be
done every day without breaking your piggy bank.
Mac OS X 10.4 Tiger, as all Unix-based systems, does not execute
those dreaded .exe files, no matter where they are or what they
want to do. Mac users who run Virtual PC can open .exe files, but
they will only run in the emulated Windows environment.
Another thing you shouldn't worry about is virus software. As of
today, there are no reported virus threats to Mac OS X.
Still, there are a few things you should be aware of to protect
your security and privacy. Starting from the default system
installation, you can act immediately.
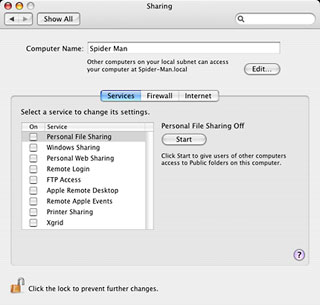
When you are connected to the Internet, it is important to limit
the number of open ports. Each open port is a potential security
hole for hackers to exploit for invasion or file transfer.
Therefore, you should only open those you need and open them only
when you actually need them for file sharing, networking, etc.
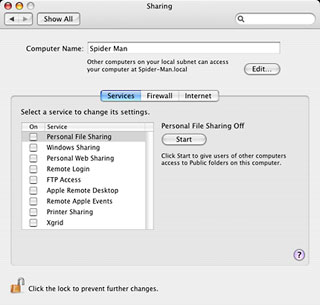 OS X has an integrated
software firewall, which you can easily use. To manage it and shut
some ports down, pull down the Apple menu in the Finder and select
System Preferences. Click on the Sharing button. Under the Services
tab you will see a number of services, most of them for sharing.
Make sure that they are all turned off - except when you really
need to use them. If you use them only once in a while, turn them
on every once in a while. It's more secure than keeping them open
at all times.
OS X has an integrated
software firewall, which you can easily use. To manage it and shut
some ports down, pull down the Apple menu in the Finder and select
System Preferences. Click on the Sharing button. Under the Services
tab you will see a number of services, most of them for sharing.
Make sure that they are all turned off - except when you really
need to use them. If you use them only once in a while, turn them
on every once in a while. It's more secure than keeping them open
at all times.
Now, click on the Firewall tab. Most of the options won't be
clickable because they are managed by the Services tab, but they
are part of them firewall anyway. Others, such as iChat Bonjour,
the network clock, and iTunes and iPhoto sharing can be turned on
and off there. The iChat Bonjour port is very likely to be one that
you keep turned on at all times if you use iChat every day.
Otherwise, the same rule applies: turn it off.
Do the same drill with the Internet tab.
 While you're still in
the System Preferences, click on Show All, and then click on
Spotlight. That's right: Spotlight can be part of your security
strategy, mostly by limiting some of its search capabilities. If
you want, for example, to make sure that your email is not
searchable, uncheck the Mail item. Do the same for all sensitive
file types.
While you're still in
the System Preferences, click on Show All, and then click on
Spotlight. That's right: Spotlight can be part of your security
strategy, mostly by limiting some of its search capabilities. If
you want, for example, to make sure that your email is not
searchable, uncheck the Mail item. Do the same for all sensitive
file types.
Still in the Spotlight preference pane, click on Privacy. You
can blacklist folders and directories to prevent Spotlight from
searching them by clicking on the plus sign (+) button in the
bottom left corner of the window.
Kick Butt with a Single
Password
Mac OS X brought a solid amount of security to the Mac by coming
up with a good user and password interface. By allowing a
computer's owner to administrate everything with accounts, it
addressed security concerns. The admin password can prevent
unwanted software from installing itself, virtually eliminating any
spyware threats. Of course, minimizing the number of admin accounts
is always smart.
 The other
advantage of accounts is that you can easily lock your computer by
logging out before leaving. Another way to lock your computer is to
make sure that the default screen saver activates when you are away
and requires the user password to authorize access again.
The other
advantage of accounts is that you can easily lock your computer by
logging out before leaving. Another way to lock your computer is to
make sure that the default screen saver activates when you are away
and requires the user password to authorize access again.
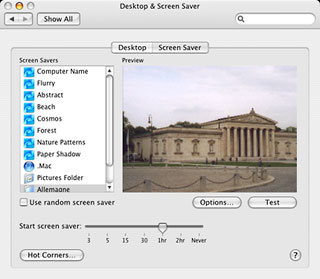
To set this up, go to the System Preferences and click on
Desktop & Screen Saver. Click on the Screen Saver tab. Then,
choose when you want the screen saver to take over when you are
leaving. Click on the Hot Corners button if you want one of the
screen corners to be used as a screen saver launcher. If you do
that, rolling your mouse to the activated corner will launch the
screen saver instantly.
 Once that is done, you have
to turn on password protection. Click on Show All in the System
Preferences and choose Security. Click the checkbox besides
“Require password to wake up computer from sleep or screen
saver”. You guessed it, the setting will also ask for a
password when waking the computer up from the sleep mode.
Once that is done, you have
to turn on password protection. Click on Show All in the System
Preferences and choose Security. Click the checkbox besides
“Require password to wake up computer from sleep or screen
saver”. You guessed it, the setting will also ask for a
password when waking the computer up from the sleep mode.
While at it, take a look at the other checkboxes to see if any
of them is interesting to you. They add some robustness to your
security strategy.
Now, on top of the same Security preference pane, there is this
FileVault feature.
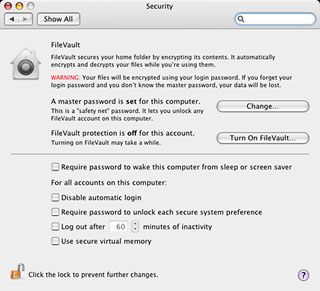 Should you use it?
Yes and no. It provides encryption for files stored in your Home
directory, making the directory a secure place to store sensitive
data. At the same time, it poses a serious threat for data
loss!
Should you use it?
Yes and no. It provides encryption for files stored in your Home
directory, making the directory a secure place to store sensitive
data. At the same time, it poses a serious threat for data
loss!
Why? Because FileVault encrypts the files and decrypts them when
you need to use them. It ties the use of your files to your
account's password - even if they are copied to another medium than
your hard drive. If you forget your password, you can kiss your
data goodbye unless you know how to crack the encryption. Good
luck....
This brings me to the importance of a good password for
efficiency, for FileVault or for just any password on the Internet.
Don't be naive: a four-letter word without numbers is easier to
crack than a long password that combines letters and numbers. In
fact, each character makes a cracker's life more difficult,
especially when numbers are thrown into the mix. If
"la32duh98" is harder to remember than "blah", it's also much more
secure.
Internet Cleanup
Are you paranoid about security yet? Good. I am, and I have some
more suggestions.
Buy Internet Cleanup from Allume, and for a relatively low price
(US$29.99) you'll get more options to protect yourself against
unwanted intruders and hackers.
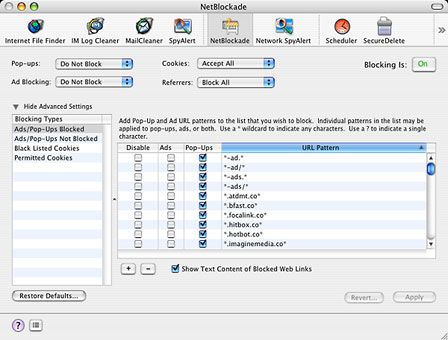
Its NetBlockade feature will address many concerns. It will come
down on browser popups like a ton of bricks, and it will also crack
down on unwanted advertising. It lets you tailor your preferences
for cookies that websites install to track your surfing habits. My
favorite feature of all: NetBlockade can refuse to give away the
last Web pages you have visited when you head to another site. I
told you I was paranoid....
The NetBlockade feature be combined with (or override) your
browser's privacy and security features to make browsing more
secure. It is highly customizable, down to the names of servers
that should be allowed to show popup windows and ads.
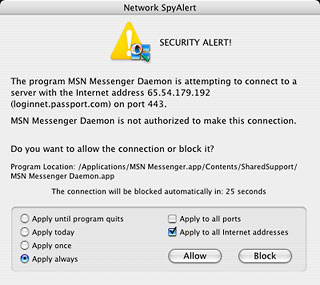
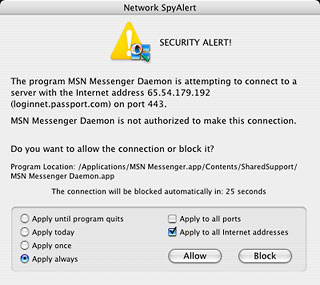 Network SpyAlert is another
neat feature of Internet Cleanup. It intercepts all network
activity and asks you what to do about them. Therefore, you can
decide what software can contact which server. When you first use
it, it will be quite aggressive. But don't worry, this happens
because it has no authorizations to remember when you first install
it.
Network SpyAlert is another
neat feature of Internet Cleanup. It intercepts all network
activity and asks you what to do about them. Therefore, you can
decide what software can contact which server. When you first use
it, it will be quite aggressive. But don't worry, this happens
because it has no authorizations to remember when you first install
it.
Tailor its authorizations as the alerts appear, and it will
remember which Internet addresses are considered safe to contact
temporarily or at any time. At that point, only unwanted
connections will be detected for you to block. I strongly recommend
using the feature, because it prevents software from reporting
activity without your authorization.
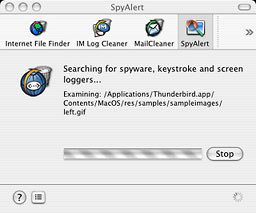
SpyAlert is another nice safeguard against intrusions. It scans
your computer for spyware. Since there is no effective spyware for
the Mac at the moment, it doesn't find anything yet, but since it
is included in an inexpensive package, it's nice to have,
especially if threats materialize.
Internet Cleanup also includes cleaning options, but in my
series of tutorials about Mac maintenance, you learned how to do
that kind of work. In any case, Internet Cleanup offers you another
way to do it.
Awareness
The last step in computer security is awareness. Yes, your mind
is important. There are some small things you can do to prevent
problems.
The first tip? Use plain text email. By doing away with HTML,
you get rid of JavaScript and code that execute automatically when
read. You also make sure that no 'tracker' image proves that you
opened a spam message.
Phishing, a technique used to fool you into giving your personal
and financial information to thieves who pretend to be from your
bank, PayPal, eBay, etc. is easier to avoid with plain text email.
That's because HTML allows thieves to code a phishing link to
make it look legitimate. Plain text strips the thief from the
"clothes" he uses to hide - to let you see that the link you are
supposed to follow is not legit.
 Secondly, I strongly
recommend that you download security updates whenever they are
available in the System Preferences (when there, click on the
Software Update button to get them). Look for all software update
descriptions to see if there are security fixes elsewhere than in
the security updates. For instance, an AirPort update can contain
security fixes. For non-Apple software, make sure to check the
vendors' websites to find similar updates.
Secondly, I strongly
recommend that you download security updates whenever they are
available in the System Preferences (when there, click on the
Software Update button to get them). Look for all software update
descriptions to see if there are security fixes elsewhere than in
the security updates. For instance, an AirPort update can contain
security fixes. For non-Apple software, make sure to check the
vendors' websites to find similar updates.
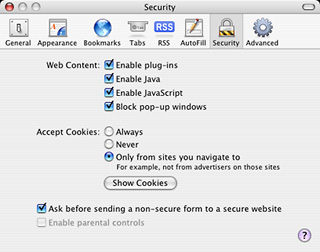
Using a browser with good security preferences is another smart
thing to do. Most Mac browsers are good, with extra kudos for
Opera, which is a gem in that department. Not using the autofill
and autocomplete features also prevents Web forms from being filled
in automatically.

When you browse, notice which pages are secure and which are
not. Secure pages start with https instead of plain http, and
browsers will change the color of the address bar as well as
display a locked padlock. Another important setting is to allow
your browser to display an alert that lets you know when you leave
a secure browsing area right in the middle of a transaction. Don't
turn this off! Sites that lie about security and encryption will be
uncovered easily when the alert shows up.
It sounds stupid, but it's still true: Email attachments should
always be handled with care. When they come from trusted sources,
they are usually free from any threats, but you should still be
careful, especially with Microsoft Word files, which can contain
macro viruses. Make sure to have macro virus protection turned on
in Word. Pull down the Word menu, select Preferences, and click on
Security, and then check "Warn before opening files that contain
macros"
One last tip: Erase file securely – by overwriting them -
in the Finder by pulling down the Finder menu and choosing Secure
Empty Trash. That way, nobody will be able to recuperate them.
Nobody said that you had to deal with cracking, hacking, spam
and security holes just because you use a computer. Leave that to
Windows users. There is nothing better to satisfy your security
paranoia than using a Macintosh. :-)
Michel Munger is a journalist who lives in Montréal. He discovered the Mac in 1994, and his work on a PC reminds him every day why he embraced Apple's platform. Munger has also authored some MacDaniel columns.


 OS X has an integrated
software firewall, which you can easily use. To manage it and shut
some ports down, pull down the Apple menu in the Finder and select
System Preferences. Click on the Sharing button. Under the Services
tab you will see a number of services, most of them for sharing.
Make sure that they are all turned off - except when you really
need to use them. If you use them only once in a while, turn them
on every once in a while. It's more secure than keeping them open
at all times.
OS X has an integrated
software firewall, which you can easily use. To manage it and shut
some ports down, pull down the Apple menu in the Finder and select
System Preferences. Click on the Sharing button. Under the Services
tab you will see a number of services, most of them for sharing.
Make sure that they are all turned off - except when you really
need to use them. If you use them only once in a while, turn them
on every once in a while. It's more secure than keeping them open
at all times. While you're still in
the System Preferences, click on Show All, and then click on
Spotlight. That's right: Spotlight can be part of your security
strategy, mostly by limiting some of its search capabilities. If
you want, for example, to make sure that your email is not
searchable, uncheck the Mail item. Do the same for all sensitive
file types.
While you're still in
the System Preferences, click on Show All, and then click on
Spotlight. That's right: Spotlight can be part of your security
strategy, mostly by limiting some of its search capabilities. If
you want, for example, to make sure that your email is not
searchable, uncheck the Mail item. Do the same for all sensitive
file types.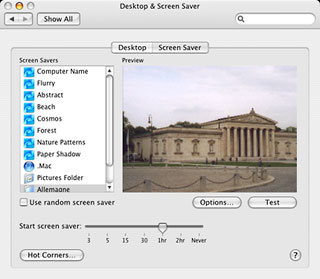 The other
advantage of accounts is that you can easily lock your computer by
logging out before leaving. Another way to lock your computer is to
make sure that the default screen saver activates when you are away
and requires the user password to authorize access again.
The other
advantage of accounts is that you can easily lock your computer by
logging out before leaving. Another way to lock your computer is to
make sure that the default screen saver activates when you are away
and requires the user password to authorize access again.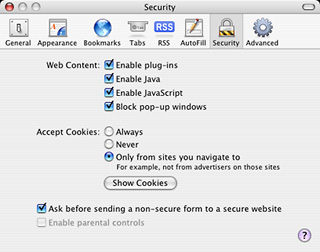 Once that is done, you have
to turn on password protection. Click on Show All in the System
Preferences and choose Security. Click the checkbox besides
“Require password to wake up computer from sleep or screen
saver”. You guessed it, the setting will also ask for a
password when waking the computer up from the sleep mode.
Once that is done, you have
to turn on password protection. Click on Show All in the System
Preferences and choose Security. Click the checkbox besides
“Require password to wake up computer from sleep or screen
saver”. You guessed it, the setting will also ask for a
password when waking the computer up from the sleep mode.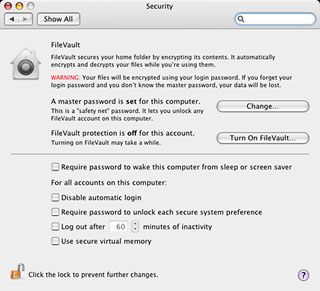 Should you use it?
Yes and no. It provides encryption for files stored in your Home
directory, making the directory a secure place to store sensitive
data. At the same time, it poses a serious threat for data
loss!
Should you use it?
Yes and no. It provides encryption for files stored in your Home
directory, making the directory a secure place to store sensitive
data. At the same time, it poses a serious threat for data
loss!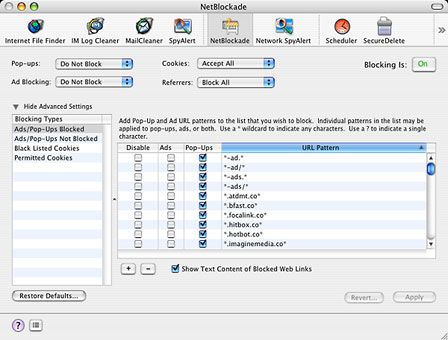
 Network SpyAlert is another
neat feature of Internet Cleanup. It intercepts all network
activity and asks you what to do about them. Therefore, you can
decide what software can contact which server. When you first use
it, it will be quite aggressive. But don't worry, this happens
because it has no authorizations to remember when you first install
it.
Network SpyAlert is another
neat feature of Internet Cleanup. It intercepts all network
activity and asks you what to do about them. Therefore, you can
decide what software can contact which server. When you first use
it, it will be quite aggressive. But don't worry, this happens
because it has no authorizations to remember when you first install
it.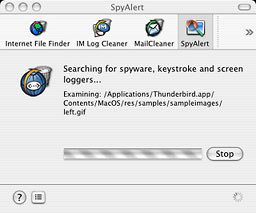
 Secondly, I strongly
recommend that you download security updates whenever they are
available in the System Preferences (when there, click on the
Software Update button to get them). Look for all software update
descriptions to see if there are security fixes elsewhere than in
the security updates. For instance, an AirPort update can contain
security fixes. For non-Apple software, make sure to check the
vendors' websites to find similar updates.
Secondly, I strongly
recommend that you download security updates whenever they are
available in the System Preferences (when there, click on the
Software Update button to get them). Look for all software update
descriptions to see if there are security fixes elsewhere than in
the security updates. For instance, an AirPort update can contain
security fixes. For non-Apple software, make sure to check the
vendors' websites to find similar updates.

